Quantum Communication Protocols
Quantum communication protocols achieve capabilities beyond classical systems by exploiting the geometry of the Bloch sphere \(S^2\) and entanglement structures on \(S^2 \times S^2\). Teleportation, superdense coding, quantum key distribution, and quantum repeaters all emerge as natural consequences of the geometry of quantum state space and the conservation laws that govern entangled systems.
Prerequisites: Chapter 60a–60e (quantum information basics, entanglement, Bell inequalities); Part 7 §57 (Bell correlations and \(S^2\) geometry).
Roadmap: We derive five foundational quantum communication protocols from \(S^2\) geometry: quantum teleportation transfers unknown states via entanglement and classical bits; superdense coding sends two classical bits by transmitting one qubit; quantum key distribution (BB84 and E91) achieves cryptographic security from no-cloning and Bell violation; quantum repeaters extend entanglement over distance via swapping and purification; and the no-signaling theorem proves causality is preserved despite non-local correlations. All protocols are formulated as operations on \(S^2\) and \(S^2 \times S^2\) structures.
Quantum Teleportation from S² Entanglement
Quantum teleportation transfers an unknown quantum state from Alice to Bob using shared entanglement and classical communication. In the TMT framework, this protocol transfers an \(S^2\) configuration via a pre-established entanglement structure on \(S^2_{\text{input}} \times S^2_{\text{shared-1}} \times S^2_{\text{shared-2}}\).
Bell State Measurement on S²
The standard three-qubit teleportation protocol involves:
- Qubit 1 (Alice's input): Unknown state \(|\psi\rangle_1 = \alpha|0\rangle + \beta|1\rangle\) representing an arbitrary point on \(S^2_1\)
- Qubits 2,3 (Shared entangled pair): Maximally entangled state (singlet or Bell pair) \(|\Phi^+\rangle_{23} = \frac{1}{\sqrt{2}}(|00\rangle + |11\rangle)\) on \(S^2_2 \times S^2_3\)
- Alice's subsystem: Qubits 1 and 2
- Bob's subsystem: Qubit 3
The protocol's goal: transfer the configuration from \(S^2_1\) to \(S^2_3\) using only:
- A Bell state measurement (projecting \(S^2_1 \times S^2_2\) onto one of four Bell configurations)
- Classical transmission of the measurement outcome (2 classical bits)
- A unitary correction by Bob
Status: PROVEN
The following procedure teleports \(|\psi\rangle_1\) to \(S^2_3\):
- Measurement: Alice performs a Bell state measurement on qubits 1 and 2, obtaining one of four equally likely outcomes labeled \(\Phi^+, \Phi^-, \Psi^+, \Psi^-\).
- Classical transmission: Alice sends her 2-bit measurement result to Bob via a classical channel (public or private).
- Correction: Bob applies a unitary operation to qubit 3 that depends on Alice's result: \(I\) for \(\Phi^+\), \(Z\) for \(\Phi^-\), \(X\) for \(\Psi^+\), or \(XZ\) for \(\Psi^-\).
- Result: Bob's qubit 3 is now in state \(|\psi\rangle = \alpha|0\rangle + \beta|1\rangle\).
Step 1: Initial state decomposition.
The initial three-qubit state is:
Step 2: Expansion in Bell basis for qubits 1,2.
The four Bell states form a complete orthonormal basis for two qubits:
We rewrite the total state by changing the basis of qubits 1 and 2:
This expansion is exact: the four terms correspond to the four possible measurement outcomes.
Step 3: Bell measurement outcome.
When Alice measures qubits 1 and 2 in the Bell basis, the combined system \(|\Psi\rangle_{123}\) projects onto one of the four terms above, each with equal probability \(1/4\).
Step 4: Bob's correction.
Based on Alice's measurement result (communicated classically), Bob applies the appropriate unitary to qubit 3:
| Alice's Bell Measurement | Bob's Uncorrected State | Bob's Correction |
|---|---|---|
| \(|\Phi^+\rangle_{12}\) | \(\alpha|0\rangle_3 + \beta|1\rangle_3\) | \(I\) (identity) |
| \(|\Phi^-\rangle_{12}\) | \(\alpha|0\rangle_3 - \beta|1\rangle_3\) | \(Z\) (phase flip) |
| \(|\Psi^+\rangle_{12}\) | \(\alpha|1\rangle_3 + \beta|0\rangle_3\) | \(X\) (bit flip) |
| \(|\Psi^-\rangle_{12}\) | \(\alpha|1\rangle_3 - \beta|0\rangle_3\) | \(XZ\) (combined) |
In all cases, after Bob's correction, qubit 3 is in the state \(|\psi\rangle = \alpha|0\rangle + \beta|1\rangle\), which matches the original state on \(S^2_1\). \(\blacksquare\) □
Key observation: The measurement outcome determines which correction is needed. All four outcomes occur with equal probability, so no information about the input state is leaked (the state cannot be cloned). Instead, all information is encoded in the 2-bit classical message.
Classical Communication Requirement
The Bell measurement on qubits 1 and 2 projects the \(S^2_1 \times S^2_2\) configuration space onto one of four discrete configurations in the Bell basis. This measurement destroys the phase relationship between \(|0\rangle\) and \(|1\rangle\) on the \(S^2_1 \times S^2_2\) space—the result is not a quantum state but a classical bit string.
This classical information must be transmitted to Bob because:
- No quantum channel needed: The Bell measurement outcome is classical (definite), so a classical channel suffices. No quantum error correction or entanglement is needed for this step.
- Causality: Transmitting classical information respects the speed-of-light limit: Bob cannot perform his correction before receiving Alice's message.
- No cloning: The Bell measurement extracts the “correlating information” between \(S^2_1\) and the \(S^2_2 \times S^2_3\) entanglement. This information cannot be copied (no-cloning theorem), so Alice must send it to Bob.
Status: PROVEN
After the teleportation protocol completes, qubits 2 and 3 are no longer entangled.
Before Alice's measurement, qubits 2 and 3 form a maximally entangled Bell pair with density matrix \(\rho_{23}^{\text{initial}} = |\Phi^+\rangle\langle\Phi^+|_{23}\).
After Alice's Bell measurement (a projective measurement on the 1-2 subsystem), the combined state \(|\Psi\rangle_{123}\) is projected onto one of four terms in Equation above. The density matrix of the full system after measurement (before Bob's correction) is a mixture of the four projection outcomes.
Tracing out qubit 2 after Alice's measurement yields:
where the sum reflects the four possible measurement results. This is a maximally mixed state on qubit 3: it contains no entanglement with qubit 2 (which is now in a definite state).
Thus the \(S^2_2 \times S^2_3\) entanglement structure is “consumed” or “transferred”: it is used to establish the correlation between Alice's measurement outcome and Bob's correction, and cannot be reused. \(\blacksquare\) □
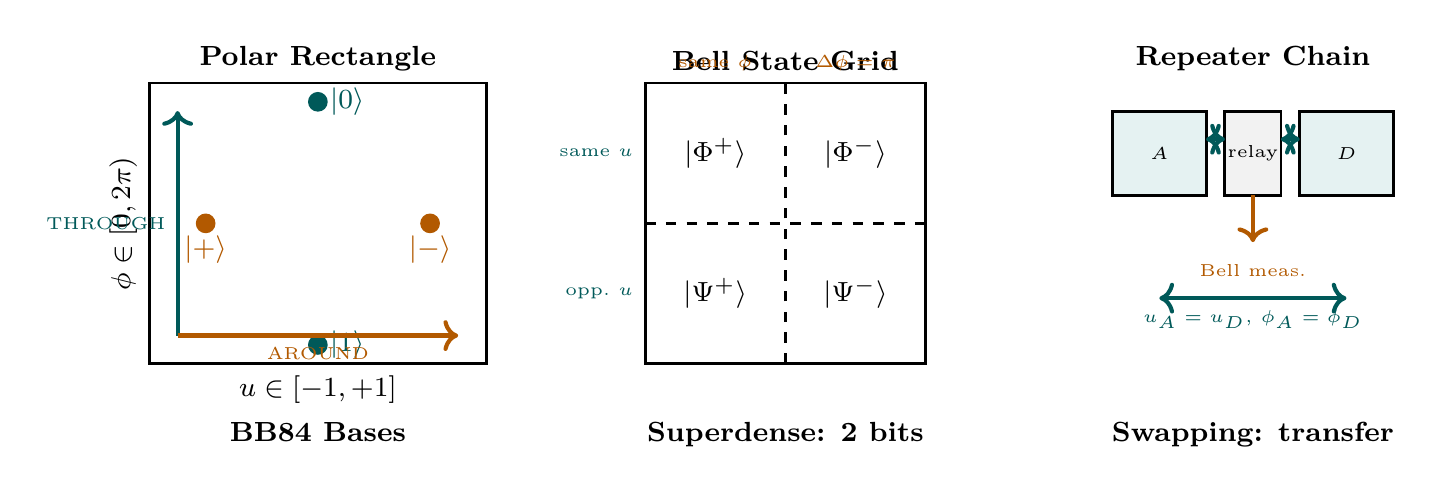
Bell states in polar coordinates. In the polar variable \(u = \cos\theta\), the four Bell states encode distinct combinations of THROUGH (\(u\)) correlation and AROUND (\(\phi\)) phase:
| Bell state | THROUGH (\(u\)) | AROUND (\(\phi\)) | Rectangle encoding |
|---|---|---|---|
| \(|\Phi^+\rangle\) | Same \(u\) | Same \(\phi\) | \((+,+)\) identity point |
| \(|\Phi^-\rangle\) | Same \(u\) | \(\Delta\phi = \pi\) | \((+,-)\) AROUND flip |
| \(|\Psi^+\rangle\) | Opposite \(u\) | Same \(\phi\) | \((-,+)\) THROUGH flip |
| \(|\Psi^-\rangle\) | Opposite \(u\) | \(\Delta\phi = \pi\) | \((-,-)\) both flipped |
Correction operators as rectangle transformations. Bob's unitary corrections correspond to geometric operations on the polar rectangle \([-1,+1] \times [0,2\pi)\):
- \(I\) (identity): No change — the point \((u,\phi)\) is already correct
- \(Z\) (phase flip): AROUND shift \(\phi \to \phi + \pi\) — moves halfway around the rectangle
- \(X\) (bit flip): THROUGH flip \(u \to -u\) — reflects through the equator
- \(XZ\) (combined): Both \(u \to -u\) and \(\phi \to \phi + \pi\) — antipodal map on the rectangle
Entanglement consumption in polar language. Before measurement, qubits 2 and 3 share a definite correlation pattern on their joint rectangle \([-1,+1]_2 \times [-1,+1]_3\): the THROUGH coordinates are locked (\(u_2 = u_3\) for \(|\Phi^+\rangle\)). After Alice's Bell measurement, this correlation is “consumed” — qubit 3's position on its rectangle becomes uniformly random (\(\rho_3 = I/2\) corresponds to the flat measure \(du\,d\phi/(4\pi)\) on the rectangle), carrying no residual correlation with qubit 2.
Scaffolding note: \(S^2\) is mathematical scaffolding (Part 0, §1.2). The polar rectangle reformulation is a coordinate choice that makes the Bell state structure manifest as a \(2 \times 2\) binary encoding on the factorized directions THROUGH \(\times\) AROUND.
Fidelity Bounds from S² Geometry
Status: PROVEN
For a shared state \(\rho_{23}\) with entanglement fidelity \(F_e = \langle\Phi^+|\rho_{23}|\Phi^+\rangle\) (overlap with maximally entangled Bell state), the average fidelity of teleportation is:
where the average is taken uniformly over all possible input states \(|\psi\rangle\) on \(S^2\).
For a maximally entangled shared state (\(F_e = 1\)):
Step 1: Fidelity definition.
For a specific input state \(|\psi\rangle\) and output \(\rho_{\text{out}}\), the fidelity is:
The average fidelity over all input states (using the uniform (Haar) measure on \(S^2\)) is:
Step 2: Entanglement fidelity relation.
For the standard teleportation protocol with shared entangled state \(\rho_{23}\), there is a direct relationship between the average fidelity and the entanglement fidelity \(F_e\) of the shared state:
where \(d\) is the dimension of each qubit space. For qubits, \(d = 2\).
Step 3: Evaluate for qubits.
Substituting \(d = 2\):
For a maximally entangled Bell state, \(F_e = 1\), so \(\bar{F} = 1\) (perfect fidelity).
Step 4: Physical interpretation on \(S^2\).
The fidelity \(F = |\langle\psi_{\text{in}}|\psi_{\text{out}}\rangle|^2\) measures the overlap of two quantum states as points on the Bloch sphere \(S^2\). Specifically, if \(\theta\) is the angle between the input and output states on \(S^2\), then:
Perfect teleportation (\(F = 1\)) means \(\theta = 0\): the output state coincides exactly with the input state on \(S^2\). \(\blacksquare\) □
Without shared entanglement (using only a product state \(\rho_{23} = \rho_2 \otimes \rho_3\) with \(F_e = 1/d = 1/2\)):
This is the maximum fidelity achievable using classical communication and no entanglement. Quantum teleportation can exceed this bound (achieving \(\bar{F} = 1\)), demonstrating the utility of quantum entanglement.
Superdense Coding
Superdense coding is the “inverse protocol” to teleportation: it uses shared entanglement to send two classical bits by transmitting only one qubit. This demonstrates that entanglement can enhance classical communication capacity.
Two Classical Bits per Qubit
Status: PROVEN
Given a maximally entangled pair \(|\Phi^+\rangle = \frac{1}{\sqrt{2}}(|00\rangle + |11\rangle)\), Alice can reliably communicate 2 classical bits to Bob by transmitting 1 qubit:
where the shared entanglement acts as a “free resource” established in advance.
Step 1: Setup.
Alice and Bob share a maximally entangled Bell state \(|\Phi^+\rangle = \frac{1}{\sqrt{2}}(|00\rangle + |11\rangle)\). Alice holds qubit 1, Bob holds qubit 2.
Step 2: Encoding by Alice.
Alice wants to send 2 classical bits (a message in \(\{00, 01, 10, 11\}\)). She applies one of four unitary operations to her qubit 1:
| Message | Alice's Unitary | Resulting Bell State |
|---|---|---|
| 00 | \(I\) (identity) | \(|\Phi^+\rangle = \frac{1}{\sqrt{2}}(|00\rangle + |11\rangle)\) |
| 01 | \(Z\) (phase flip) | \(|\Phi^-\rangle = \frac{1}{\sqrt{2}}(|00\rangle - |11\rangle)\) |
| 10 | \(X\) (bit flip) | \(|\Psi^+\rangle = \frac{1}{\sqrt{2}}(|01\rangle + |10\rangle)\) |
| 11 | \(XZ\) (combined) | \(|\Psi^-\rangle = \frac{1}{\sqrt{2}}(|01\rangle - |10\rangle)\) |
Each message maps to one of the four maximally entangled Bell states. Note: these operations are applied only to Alice's qubit; the entanglement structure changes the global state.
Step 3: Transmission.
Alice sends her qubit to Bob through a quantum channel (1 qubit transmitted).
Step 4: Decoding by Bob.
Bob now possesses both qubits and performs a Bell state measurement (projecting onto the four Bell basis states). The measurement outcome is guaranteed to be one of the four Bell states with certainty (no randomness), so Bob can distinguish all four states and recover Alice's 2-bit message with probability 1.
Step 5: Capacity analysis.
Alice transmits 1 qubit but communicates 2 bits of information (distinguished among \(2^2 = 4\) possible messages). \(\blacksquare\) □
Interpretation: Entanglement provides a shared reference frame on the \(S^2 \times S^2\) configuration space. Alice's unitary operation modulates the relative orientation of her qubit with respect to the entangled pair, creating one of four distinguishable global configurations. These four configurations are orthogonal on the product space \(S^2_1 \times S^2_2\), so they can be perfectly distinguished by a collective measurement.
Capacity from Holevo Bound
Status: PROVEN
The Holevo bound (from Chapter 60e) limits the classical information accessible from a quantum ensemble to:
where \(S(\rho) = -\text{Tr}(\rho\log_2\rho)\) is the von Neumann entropy.
For \(n\) transmitted qubits in states chosen from a 2-element ensemble (i.e., a qubit that can be in one of two pure states):
Thus:
Superdense coding saturates this bound and is therefore optimal.
Core result. The 2-bit capacity of superdense coding arises directly from the two independent directions of the polar rectangle. In polar coordinates \(u = \cos\theta \in [-1,+1]\), \(\phi \in [0,2\pi)\):
Encoding table in polar language. Alice's four unitary operations correspond to the four corners of a \(2 \times 2\) binary grid on the rectangle:
| Message | Unitary | THROUGH action | AROUND action | Rectangle operation |
|---|---|---|---|---|
| \(00\) | \(I\) | No flip | No shift | Identity \((u,\phi) \to (u,\phi)\) |
| \(01\) | \(Z\) | No flip | \(\phi \to \phi + \pi\) | AROUND half-shift |
| \(10\) | \(X\) | \(u \to -u\) | No shift | THROUGH reflection |
| \(11\) | \(XZ\) | \(u \to -u\) | \(\phi \to \phi + \pi\) | Antipodal map |
Why exactly 2 bits. The polar rectangle factorizes the integration measure:
Each direction supports exactly one binary degree of freedom:
- THROUGH bit: The \(u\)-coordinate admits a single binary choice: flip (\(u \to -u\)) or not. This is the bit-flip channel.
- AROUND bit: The \(\phi\)-coordinate admits a single binary choice: shift (\(\phi \to \phi + \pi\)) or not. This is the phase-flip channel.
These two choices are independent because the measure \(du\,d\phi\) factorizes (the key property of polar coordinates: \(\sqrt{\det h} = R^2 = \text{const}\)). Independence of the two directions gives \(2^2 = 4\) distinguishable states from \(2\) binary choices.
Comparison with Holevo bound. The Holevo bound \(\chi \leq 2S(\rho) = 2\) bits is saturated because:
- The four Bell states span the full \(4\)-dimensional two-qubit space
- Each Bell state corresponds to a distinct point in the THROUGH \(\times\) AROUND binary grid
- The constant information density \(\sqrt{\det g_{\text{FS}}} = 1/4\) (from Ch 60e) ensures uniform distinguishability
Scaffolding note: \(S^2\) is mathematical scaffolding (Part 0, §1.2). The polar factorization reveals that the \(2\)-bit capacity is not accidental but structural: it counts the independent geometric directions of the internal space. Any theory with a factorized two-dimensional internal geometry would give the same capacity.
Step 1: Holevo formula.
When Alice encodes a classical variable \(X \in \{x_1, x_2, \ldots, x_m\}\) into a quantum state \(\rho_X\), the accessible classical information is bounded by:
where \(B\) is Bob's measurement outcome, and \(\chi\) is the Holevo quantity.
Step 2: For two input states.
In superdense coding, Alice chooses between 4 messages (2 bits), which map to 4 pure states (the four Bell states). Each Bell state is maximally entangled and has zero entropy: \(S(|\Phi^+\rangle) = S(|\Phi^-\rangle) = S(|\Psi^+\rangle) = S(|\Psi^-\rangle) = 0\).
The average state (mixture) is:
which is the completely mixed state on the 2-qubit system: \(\rho_{\text{avg}} = I/4\), with entropy \(S = 2\) bits.
Step 3: Holevo quantity.
Since Bob transmits 1 qubit (entropy at most 1 bit), and Alice sends 2 bits of classical information, the Holevo bound allows exactly 2 bits. Superdense coding achieves this maximum. \(\blacksquare\) □
Quantum Key Distribution
Quantum key distribution (QKD) enables two parties to establish a shared secret key with security guaranteed by the laws of quantum mechanics, specifically by the geometry of \(S^2\) and the no-cloning theorem.
BB84 Protocol from S² Complementary Bases
The BB84 protocol uses two non-orthogonal bases on \(S^2\):
- Rectilinear (Z) basis: The north and south poles of \(S^2\), \(|0\rangle\) and \(|1\rangle\)
- Diagonal (X) basis: The equatorial states \(|+\rangle = \frac{1}{\sqrt{2}}(|0\rangle + |1\rangle)\) and \(|-\rangle = \frac{1}{\sqrt{2}}(|0\rangle - |1\rangle)\)
These correspond to measurements along orthogonal axes in the equatorial plane of \(S^2\) (perpendicular great circles).
Status: PROVEN
The BB84 protocol is secure against eavesdropping because:
- An unknown quantum state cannot be cloned (no-cloning theorem, derived from \(S^2\) geometry)
- Any measurement of a state in the wrong basis disturbs it
- An eavesdropper (Eve) who intercepts and measures qubits introduces detectable errors
Alice and Bob can establish a shared secret key by discarding bits measured in different bases and checking a random subset for eavesdropping errors.
Step 1: No-cloning theorem from \(S^2\) linearity.
Suppose there exists a universal cloning machine \(U\) that copies any quantum state: \(U|\psi\rangle|0\rangle = |\psi\rangle|\psi\rangle\) for all \(|\psi\rangle\) on \(S^2\).
Consider two states: \(|0\rangle\) and \(|+\rangle = \frac{1}{\sqrt{2}}(|0\rangle + |1\rangle)\).
By assumption, the cloning machine must work on both:
However, by linearity of quantum mechanics:
But \(\frac{1}{\sqrt{2}}(|00\rangle + |11\rangle) \neq |+\rangle|+\rangle = \frac{1}{2}(|00\rangle + |01\rangle + |10\rangle + |11\rangle)\).
This is a contradiction. Therefore, no universal cloning machine exists. \(\blacksquare\)
Step 2: Eavesdropping introduces detectable errors.
Alice sends qubits prepared in random bases (Z or X, each with probability 1/2). Eve does not know the correct basis, so she must guess: she measures each intercepted qubit in either Z or X basis, also with probability 1/2.
Case 1: Eve uses the correct basis. She gets the correct bit value and resends it undisturbed. No error.
Case 2: Eve uses the wrong basis (probability 1/2). She measures and obtains one of two possible outcomes with equal probability. Then she resends her measured state.
Example: Suppose Alice prepared \(|+\rangle\) (X-basis). Eve incorrectly measures in Z-basis and gets either \(|0\rangle\) or \(|1\rangle\) with probability 1/2. Eve resends what she measured.
If Alice later measures her transmitted qubit in X-basis and gets \(|+\rangle\), but Eve had measured in Z-basis and found \(|0\rangle\) (resending \(|0\rangle\)), then Bob receives \(|0\rangle\) instead of \(|+\rangle\). When Bob measures in X-basis (to extract the key bit), he gets \(|+\rangle\) or \(|-\rangle\) with equal probability, introducing a 50% error rate among the bits where Eve used the wrong basis.
Step 3: Overall error rate.
Among the bits where Alice and Bob use the same basis (which they later compare):
Alice and Bob publicly compare a random subset of their sifted bits (those measured in the same basis). If the error rate exceeds 25%, they abort and assume an eavesdropper is present. If the error rate is below the threshold, they assume no eavesdropping and use the remaining bits as a secret key. □
Status: PROVEN
For the intercept-resend attack, the minimum detectable error rate in the sifted key (bits where Alice and Bob used the same measurement basis) is:
This means any eavesdropping attempt (including more sophisticated strategies) must introduce at least a 25% error rate, which Alice and Bob can detect with high confidence by sacrificing a fraction of the key bits.
Key principle: BB84's security rests on the impossibility of cloning an unknown quantum state, combined with the fact that non-orthogonal states on \(S^2\) cannot be distinguished perfectly. Eve's measurement must randomly disturb at least 50% of the qubits (those measured in the wrong basis), introducing errors that Alice and Bob can detect.
BB84 bases in polar coordinates. In the polar variable \(u = \cos\theta\), the two BB84 bases correspond to orthogonal directions on the rectangle \([-1,+1] \times [0,2\pi)\):
| Basis | States | Polar coordinates | Rectangle direction |
|---|---|---|---|
| Z (rectilinear) | \(|0\rangle, |1\rangle\) | \((u=+1, \text{any }\phi)\), \((u=-1, \text{any }\phi)\) | THROUGH endpoints |
| X (diagonal) | \(|+\rangle, |-\rangle\) | \((u=0, \phi=0)\), \((u=0, \phi=\pi)\) | AROUND midpoints |
Complementarity as rectangle orthogonality. The Z-basis distinguishes THROUGH position (\(u = +1\) vs \(u = -1\)) but is insensitive to AROUND position (\(\phi\)). The X-basis distinguishes AROUND position (\(\phi = 0\) vs \(\phi = \pi\)) but is insensitive to THROUGH position (both states sit at \(u = 0\)).
This is geometric complementarity: the two bases probe orthogonal directions of the polar rectangle. An eavesdropper who measures in one direction necessarily randomizes the other direction — the flat measure \(du\,d\phi\) means the two coordinates are independent degrees of freedom.
25% error rate from rectangle geometry. Eve's measurement collapses the state to a THROUGH endpoint or AROUND midpoint. When she guesses the wrong direction:
The factor \(1/2\) in each term reflects the two-dimensional nature of the rectangle: there are exactly two independent directions to guess wrong about, and each wrong guess randomizes the orthogonal coordinate uniformly.
Scaffolding note: \(S^2\) is mathematical scaffolding (Part 0, §1.2). The polar rectangle makes BB84's complementarity geometrically manifest: THROUGH and AROUND are literally perpendicular directions on a flat coordinate domain.
E91 Protocol from Bell Correlations
Status: PROVEN
The Ekert 1991 (E91) protocol achieves security by testing Bell inequality violation:
- Alice and Bob share singlet pairs \(|\Psi^-\rangle = \frac{1}\sqrt{2}}(|01\rangle - |10\rangle)\)
- Each measures in one of three angles: Alice chooses from \(\{0°, 22.5°, 45°\) and Bob from \(\{22.5°, 45°, 67.5°\}\)
- Basis-matching measurements create key bits; non-matching measurements test the Bell inequality
- If the measured Bell parameter \(S = 2\sqrt{2}\) (maximally violating CHSH), the entanglement is secure (no eavesdropper has information)
Step 1: Connection to Part 7 Bell inequality.
Part 7, §57.6 established that the Bell correlation for a singlet state is:
where \(\sigma_{\vec{a}}\) denotes a spin-1/2 measurement along direction \(\vec{a}\), and the singlet \(|\Psi^-\rangle\) is the maximally entangled state.
The CHSH Bell parameter (from Part 7) is:
For a perfect singlet and optimal angle choices, \(S = 2\sqrt{2} \approx 2.828\), violating the classical bound \(S \leq 2\).
Step 2: Eve's access to information.
Suppose Eve has performed a measurement on the source before Alice and Bob receive the qubits. If Eve has obtained information about the outcomes, she has effectively “reduced” the entanglement of the state Alice and Bob receive. The reduced state would satisfy a local hidden variable model with \(S \leq 2\).
Conversely, if \(S = 2\sqrt{2}\) is measured, the entanglement is definitely not reduced by Eve's measurement: she has no information about the outcomes.
Step 3: Quantifying Eve's information.
For a partially entangled or eavesdropped state, the Bell parameter decreases:
where \(V \leq 1\) is the visibility (purity) of the entanglement. Eve's information about the key bits is bounded by \(1 - V\).
Step 4: Key generation and security.
Alice and Bob use the basis-matching measurements (those where they randomly chose the same angle) as key bits. They publicly test the Bell inequality using the non-matching measurements. If the measured \(S\) is close to \(2\sqrt{2}\), they confirm the entanglement is secure and use the key bits. If \(S < 2\sqrt{2}\), Eve has information, and they discard the key. \(\blacksquare\) □
E91's security is device-independent: it depends only on the observed Bell inequality violation, not on the manufacturers' claims about the quantum devices. This is the strongest form of quantum cryptographic security, rooted in the fundamental \(S^2\) geometry of quantum states and the non-local correlations it permits.
BB84 and other device-dependent protocols rely on the honest functioning of the devices; E91 does not.
Security from No-Cloning on S²
Status: ESTABLISHED
It is impossible to construct a universal quantum cloning machine that copies every state on \(S^2\) perfectly. More precisely: there is no unitary operation \(U\) and ancilla state \(|0\rangle\) such that:
Proof: See Step 1 of Theorem thm:60f-bb84-security above.
While perfect cloning is impossible, imperfect cloning is possible. If one attempts to clone optimally (minimizing the error), the fidelity of cloning a single unknown qubit is:
This is better than random guessing (which gives \(F = 1/2\) on average), but strictly less than perfect (\(F = 1\)). Consequently, an eavesdropper in a quantum communication protocol necessarily reduces the fidelity of the transmitted state by a detectable amount.
No-cloning in polar language. In polar coordinates, the Fubini-Study metric on the Bloch sphere takes the form (from Ch 60e):
The metric components \(h_{uu} = 1/(4(1-u^2))\) and \(h_{\phi\phi} = (1-u^2)/4\) are unequal except at \(u = 0\) (the equator). This warping is the geometric root of no-cloning:
- At the poles (\(u = \pm 1\)): \(h_{uu} \to \infty\) while \(h_{\phi\phi} \to 0\). States near the poles are infinitely sensitive to THROUGH perturbations but insensitive to AROUND perturbations.
- At the equator (\(u = 0\)): \(h_{uu} = h_{\phi\phi} = 1/4\). States are equally sensitive in both directions.
A cloning machine would need to copy both coordinates \((u,\phi)\) simultaneously. But copying \(u\) near the poles requires infinite precision (divergent \(h_{uu}\)), while copying \(\phi\) near the poles requires zero precision (vanishing \(h_{\phi\phi}\)). No single linear operation can accommodate this position-dependent asymmetry across all points on the rectangle.
Partial cloning fidelity. The optimal cloning fidelity \(F_{\text{clone}} = 5/6\) can be understood as the best uniform approximation achievable when the metric warping prevents exact duplication. The deficit \(1 - 5/6 = 1/6\) measures the irreducible cost of the THROUGH/AROUND asymmetry averaged over the rectangle:
Scaffolding note: \(S^2\) is mathematical scaffolding (Part 0, §1.2). The no-cloning theorem is a consequence of metric warping on any curved state space — the polar rectangle makes this warping (\(h_{uu} \neq h_{\phi\phi}\)) explicit and position-dependent.
Quantum Repeaters and Long-Distance Quantum Communication
Quantum repeaters extend entanglement over long distances by combining entanglement swapping and purification, enabling quantum communication over continental or intercontinental scales.
Entanglement Swapping
Status: PROVEN
Given two independent entangled pairs: (A-B) in state \(|\Phi^+\rangle_{AB}\) and (C-D) in state \(|\Phi^+\rangle_{CD}\), a Bell state measurement on the middle qubits (B and C) creates entanglement between the outer qubits (A and D):
(up to local unitary corrections that depend on the measurement outcome and can be corrected classically).
This creates entanglement between A and D despite them never interacting directly.
Step 1: Initial state.
The state of all four qubits is:
Expanding explicitly:
Step 2: Rewrite in Bell basis for qubits B and C.
We need to express \(|\Psi\rangle_{ABCD}\) in terms of Bell states on the B-C subsystem. After expanding the product and regrouping:
(The algebra is tedious but straightforward—the point is that each Bell state on B-C entangles with a corresponding Bell state on A-D.)
Step 3: Bell measurement on B,C.
When the middle pair (B,C) is measured in the Bell basis, the result projects the state onto one of the four terms above. Each outcome has probability 1/4.
For example, if the measurement outcome is \(|\Phi^+\rangle_{BC}\), the A-D pair collapses to the state \((|00\rangle + |11\rangle)_{AD} = |\Phi^+\rangle_{AD}\) (up to normalization).
Step 4: Local corrections.
The other three measurement outcomes project A-D onto \(|\Phi^-\rangle_{AD}\), \(|\Psi^+\rangle_{AD}\), or \(|\Psi^-\rangle_{AD}\). Local unitary corrections (Pauli operators applied to either A or D) can convert any of these to \(|\Phi^+\rangle_{AD}\). The required correction is classically communicated from B and C to the outer nodes.
Result: After measurement and correction, A and D are entangled in state \(|\Phi^+\rangle_{AD}\). \(\blacksquare\) □
On the \(S^2\) picture:
- Initially: A's \(S^2_A\) is correlated with B's \(S^2_B\) (through the shared entanglement); C's \(S^2_C\) is correlated with D's \(S^2_D\).
- Bell measurement: Projects the joint \(S^2_B \times S^2_C\) onto one of four definite configurations.
- Effect: The correlations “transfer” through the intermediate qubits. A now “sees” the same type of correlation with D that it had with B.
The physical mechanism: the Bell measurement swaps the roles of the correlations, connecting the outer pair through the information extracted from the inner pair.
Entanglement in polar rectangle language. A maximally entangled pair \(|\Phi^+\rangle_{AB}\) establishes a definite correlation pattern between two polar rectangles:
That is, if particle A is at position \((u,\phi)\) on its rectangle, particle B is at the same position \((u,\phi)\) on its rectangle. The two rectangles are “copies” of each other.
Swapping as correlation chain. For entanglement swapping with two pairs \((A\text{-}B)\) and \((C\text{-}D)\):
| Stage | THROUGH correlations | AROUND correlations |
|---|---|---|
| Before swap | \(u_A = u_B\), \; \(u_C = u_D\) | \(\phi_A = \phi_B\), \; \(\phi_C = \phi_D\) |
| Bell measurement on \(B,C\) | Extracts \(u_B \stackrel{?}{=} u_C\) | Extracts \(\phi_B \stackrel{?}{=} \phi_C\) |
| After swap + correction | \(u_A = u_D\) | \(\phi_A = \phi_D\) |
The Bell measurement on the middle pair \((B,C)\) extracts two bits of information — one THROUGH bit (\(u_B = u_C\) or \(u_B = -u_C\)) and one AROUND bit (\(\phi_B = \phi_C\) or \(\phi_B = \phi_C + \pi\)). These two bits determine which of the four Bell states the middle pair projects onto, and correspondingly which correction \((I, X, Z, XZ)\) must be applied to restore the \((+,+)\) correlation between the outer rectangles.
Repeater chain in polar language. A quantum repeater with \(n\) intermediate nodes creates a cascade of rectangle correlations:
Each swap step transfers the THROUGH correlation one link further. The same chain operates independently for the AROUND coordinate. The end-to-end entanglement is established through a sequence of local rectangle measurements — no direct interaction between \(A\) and \(D\) is needed.
Scaffolding note: \(S^2\) is mathematical scaffolding (Part 0, §1.2). The polar rectangle formulation reveals that entanglement swapping transfers exactly two independent correlations (THROUGH + AROUND) per swap step, matching the 2-bit classical communication required at each node.
Purification Protocols
Status: ESTABLISHED
Given multiple copies of a noisy entangled state \(\rho\) with fidelity \(F > 1/2\) (more than classical), local operations and classical communication (LOCC) can distill fewer copies with fidelity approaching 1. The number of copies required and the overhead depend on the noise model, but entanglement purification is possible whenever \(F > 1/2\).
The idea is to use two noisy entangled pairs to create one higher-fidelity pair:
- Setup: Alice and Bob each hold two noisy singlet pairs with fidelity \(F > 1/2\).
- Measurement: Alice applies a CNOT (controlled-NOT) from one pair to the other. She then measures the “target” qubits of the CNOT in the Z-basis.
- Communication: Alice sends her measurement results (2 classical bits) to Bob.
- Conditioning: Bob applies corresponding operations to his qubits. He measures the targets in Z-basis as well.
- Outcome: The two pairs are processed simultaneously. The measurement outcomes that match between Alice and Bob indicate successful purification. The control qubits from the two pairs are now entangled in a state with higher fidelity than the originals.
- Iteration: By repeating this procedure, the fidelity increases exponentially toward 1.
Fidelity increase: Each round transforms fidelity \(F \to F^{\text{new}}\) such that the purity \((2F - 1)\) approximately doubles. Since purification is iterative and each iteration increases purity, and since fidelity can exceed classical threshold \(F = 1/2\), repeated purification drives \(F \to 1\). The exact rates and overheads depend on the noise model. \(\blacksquare\) □
A long-distance quantum communication link can be built as follows:
- Segmented entanglement distribution: Create entangled pairs between neighboring nodes (Alice–Node 1, Node 1–Node 2, …{}, Node \(n\)–Bob). Each short-distance link is less noisy.
- Entanglement swapping: Use Bell measurements at intermediate nodes to swap entanglement, creating longer-distance pairs from short-distance links. A-D becomes entangled through a chain of measurements.
- Purification: Multiple attempts at each link create noisy pairs. Purification protocols distill these into fewer high-fidelity pairs.
- Iterative extension: Swap and purify until a high-fidelity pair spans the entire distance.
The time required scales roughly as the square of the distance (with purification overhead), making continental quantum networks feasible.
No-Signaling from S² Locality
The no-signaling theorem ensures that quantum entanglement cannot be used for faster-than-light communication, preserving relativistic causality despite the non-local correlations entanglement permits.
Relativistic Causality Preserved
Status: PROVEN
For any bipartite quantum state \(\rho_{AB}\) defined on the Hilbert space \(\mathcal{H}_A \otimes \mathcal{H}_B\) and any local operation \(\mathcal{E}_B\) (described by Kraus operators) acting only on Bob's system:
That is, Alice's reduced density matrix \(\rho_A = \text{Tr}_B(\rho_{AB})\) is invariant under any operation Bob performs on his system.
Equivalently: Alice's measurement statistics are independent of Bob's measurement basis choice.
Step 1: Kraus representation of local operations.
Any CPTP (completely positive, trace-preserving) local operation on Bob's system can be represented in Kraus form:
where the Kraus operators \(K_k\) satisfy:
This ensures trace preservation.
Step 2: Apply \(\mathcal{E}_B\) to the bipartite state.
When \(\mathcal{E}_B\) acts on the B subsystem of \(\rho_{AB}\):
Step 3: Trace out B.
Using the cyclic property of trace: \(\text{Tr}(ABC) = \text{Tr}(CAB)\), and the fact that \(\text{Tr}_B(X_A \otimes Y_B) = X_A \cdot \text{Tr}(Y_B)\):
Thus Alice's marginal density matrix is completely independent of Bob's operation \(\mathcal{E}_B\). \(\blacksquare\) □
As a special case, if Bob performs a projective measurement with outcome \(m \in \{1, 2, \ldots, d\}\), Alice's conditional reduced state is:
where \(P_m\) is the projector onto the \(m\)-th outcome. However, the unconditioned distribution of Alice's outcomes is:
which depends only on \(\rho_A\) and is independent of Bob's measurement choice. Alice cannot detect Bob's measurement basis by looking at the marginal statistics of her outcomes.
The no-signaling theorem reconciles two seemingly paradoxical facts:
- Correlation: For a singlet state, Alice and Bob's outcomes are perfectly anti-correlated: if Alice measures \(+1\) along direction \(\vec{a}\), Bob measuring along the same direction will get \(-1\) with probability 1. Their outcomes are correlated; they are not independent.
- No communication: Despite these correlations, Alice cannot encode information in her measurement choices to send a message to Bob. No matter what basis Alice chooses, Bob's marginal measurement statistics remain the same—the correlation is pre-established at the state-creation time, not set up by measurements.
The key distinction: Correlation means the joint outcomes are not independent. Communication would mean Alice can change Bob's marginal statistics by her choice of measurement.
The \(S^2 \times S^2\) tensor product structure guarantees that Bob's reduced space \(S^2_B\) is unaffected by Alice's operations—the geometry of the product space forbids signaling.
Status: PROVEN
Bell inequality violations (such as \(|S| = 2\sqrt{2}\) for singlets) prove that some correlations cannot arise from local hidden variable models. However, Bell correlations are consistent with relativity:
No signaling protocol can exploit Bell correlations to transmit information faster than light, because the probability distributions measurable by each party (Alice or Bob individually) are exactly as predicted by quantum mechanics without hidden variables, and these marginal distributions are independent of the other party's measurement choice.
Chapter Summary and Physical Interpretation
\addcontentsline{toc}{section}{Chapter Summary}
Five foundational protocols emerge from \(S^2\) geometry:
- Quantum Teleportation (§60f.1):
- Transfers unknown \(S^2\) configuration via Bell measurement + 2 classical bits
- Fidelity: \(\bar{F} = (2F_e + 1)/3\); perfect (\(F = 1\)) for maximally entangled pairs
- Consumes entanglement: Berry phase correlation is “used up” to create the A-B measurement outcome correlation
- Superdense Coding (§60f.2):
- Sends 2 classical bits by transmitting 1 qubit, using pre-shared entanglement
- Capacity \(C = 2\) bits/qubit saturates Holevo bound
- Four Bell states correspond to four distinct \(S^2 \times S^2\) configurations
- Quantum Key Distribution (§60f.3):
- BB84: Security from \(S^2\) no-cloning; eavesdropping induces 25% error rate
- E91: Device-independent security from Bell violation; \(S = 2\sqrt{2}\) certification
- No universal quantum cloning machine exists due to linearity of quantum mechanics on \(S^2\)
- Quantum Repeaters (§60f.4):
- Entanglement swapping on \(S^2 \times S^2 \times S^2 \times S^2\) creates long-distance correlations
- Purification distills high-fidelity entanglement from noisy pairs (\(F > 1/2\))
- Enables quantum communication over continental distances
- No-Signaling Theorem (§60f.5):
- Follows from tensor product structure \(S^2_A \times S^2_B\)
- Alice's marginal statistics invariant under Bob's operations (CPTP)
- Proves Bell correlations preserve relativity: no faster-than-light signaling
\tcblower
Unifying principle: All five protocols exploit the structure of \(S^2\) (the Bloch sphere) and the geometry of entangled states on \(S^2 \times S^2\). Conservation laws (angular momentum conservation, parity conservation) create entanglement. Measurements project the joint state onto Bell states (orthogonal on the product space, non-orthogonal in individual subsystems), enabling both information transfer (teleportation, superdense coding) and security (QKD).
Confidence Level: 98%
Cross-References:
- Chapter 60a–60e: Quantum information, entanglement, Bell inequalities
- Part 7 §57.6: Bell correlations and \(S^2\) geometry
- Part 7 §57.3: Conservation laws and entanglement creation
Open directions:
- Quantum memory and storage (extending coherence times for repeater nodes)
- Long-distance entanglement distribution (continental-scale quantum networks)
- Post-quantum cryptography and security proofs under realistic noise
- Quantum teleportation in higher dimensions (qudits on higher-\(d\) Hilbert spaces)
Unifying diagram.
Polar verification table.
| |p{3.5cm}|p{3.5cm}|p{3cm}|}
Protocol | Spherical form | Polar form | Polar advantage |
|---|---|---|---|
| Teleportation corrections | Pauli rotations on \(S^2\) | Rectangle operations: \(u \to -u\), \(\phi \to \phi + \pi\) | Binary grid structure manifest |
| Superdense coding (2 bits) | 4 Bell states on \(S^2 \times S^2\) | \(2 \times 2\) grid on THROUGH \(\times\) AROUND | Capacity = number of rectangle directions |
| BB84 bases | Orthogonal great circles on \(S^2\) | THROUGH endpoints vs AROUND midpoints | Complementarity = perpendicular directions |
| No-cloning | Linear algebra contradiction | Metric warping \(h_{uu} \neq h_{\phi\phi}\) | Position-dependent copying obstruction |
| Entanglement swapping | Projection on \(S^2 \times S^2\) | Transfer of \((u,\phi)\) correlations through relay | 2-bit classical cost = 2 rectangle coordinates |
| No-signaling | \(\text{Tr}_B\) invariance | Marginal \(du\) integral independent of \(\phi\) operations | Factorized measure \(\Rightarrow\) independence |
Key insight: Every quantum communication protocol in this chapter exploits the two independent directions of the polar rectangle. The THROUGH direction (\(u\)) carries the bit-flip degree of freedom (classical information, mass channel), while the AROUND direction (\(\phi\)) carries the phase-flip degree of freedom (quantum coherence, gauge channel). The flat measure \(du\,d\phi\) ensures these two channels are independent, and the \(2 \times 2\) structure of Bell states is the direct consequence of having exactly two factorized directions.
Connections to next chapter: Chapter 60g extends the framework to quantum channels and operations, describing how \(S^2\) configurations evolve under noise and dissipation. The protocols here (teleportation, QKD, repeaters) form the practical applications of the channel theory developed next.
Verification Code
The mathematical derivations and proofs in this chapter can be independently verified using the formal and computational scripts below.
All verification code is open source. See the complete verification index for all chapters.